Cybersecurity Matters: Why the Cloud Delivers Fewer Hassles for AV Firms

Once upon a time, A/V was simple. Wire it up, plug it in, and turn it on. While the analog days made for easy set-up, they also created hassles and headaches. Does your client have a problem? Guess what, you’re driving out to fix it or on the phone helping them troubleshoot. Not only did this take out of your day, it wasn’t client-focused. If something went down, they had to wait for you to come fix it.
The Changing, Connected Market for AV Services
Today, everything is digital and connected. Now, if something goes down, an error code tells you exactly what you need to do to fix it. Troubleshooting, software patches, and configuration can be done from the home office. In some cases, your products can even warn you before things start to go awry.
But not all is sunshine and rainbows. The move from analog AV to digital has opened your firm up to new threats. There’s a reason that people remember the Max Headroom signal hijacking in 1987 more than the thousands of breaches that have occurred in the AV world in the past few years—because taking over two television stations in 1987 was an incredible feat.
Nowadays, if it can be connected to the internet, it can be breached with enough labor and time, and breaches are far too common.
Hackers have breached Ring/Nest home security systems, hooligans have spent the pandemic taking advantage of lax security to participate in “Zoombombing,” and conferences have been disrupted by video board takeovers and social feed disruptions. Each of these isn’t just an example of a casual hack, these were breaches of publicly traded or multimillion-dollar organizations.
Knowing this, AV firms need to be proactive—because if hackers and criminals can break into companies with the backing of Google, a connected AV system might turn into a walk in the park. So what can you do? A recent webinar from Commercial Integrator looked to provide the answers.
Putting together a Sound Cybersecurity Strategy for AV Firms
With the risks and the stakes higher than ever, it’s amazing to think that 41% of respondents cited that they have no cybersecurity training program in place and no plans to add one. Presenting both a risk and an opportunity, AV companies need to embrace cybersecurity on both sides of the equation—not only taking steps to help employees protect systems but turning AV cybersecurity into a competitive advantage by offering services to clients.
“Now, all devices are endpoints and now, all devices are somewhat accessible on the network.” Whether it’s as direct as a physical breach (i.e. plugging a USB stick in), using an unprotected Bluetooth connection to access devices, or getting into the settings through poorly protected Wi-Fi, the threat vectors are endless—and the things accessible are sensitive.
Start with Secure Deployment
Securing your AV-over-IT is a hard job, but one that your clients need. The Commercial Integrator webinar breaks deployment into the following steps:
- Understand the Customer’s Needs, Set Expectations: Features matter, but not at the expense of security. When speaking with your customers, they have a picture of how they intend to use your solution, and you need to ask them about this. Security depends on the user base, operating environment, and risk tolerance of your client. Knowing this, your decision to increase security may result in limited functionality and decreased usability.
- Update and Maintain Firmware: One of the most dangerous thought processes in today’s landscape is “we don’t patch a working system.” This was fine when nothing was connected—if it worked, it worked—but today, you have to move from install to support.
- Only Enable What Matters: Another dangerous mentality in the connected world is the idea of leaving everything on in case it’s needed. This leaves systems open to attack. CI panelists recommend starting with everything disabled before slowly and securely adding new features, taking steps to ensure each is locked down.
- Focus on Features and Policies: You can’t actively manage everything, but with the right policies and security features in place, you can prevent unauthorized access. AES encryption ensures secure transmission, 802.1x device authentication ensures that every device on the network was explicitly authorized by the IT department, and other things like password rules and audit logging go a long way in protecting systems.
Test, Manage, and Protect
Protecting AV systems goes beyond the deployment. Successfully protecting your clients requires ongoing analysis, approval, and management. From something as simple as routinely helping clients manage their own firmware updates to focusing on the three principles of security, you can make sure your systems are locked down and your clients are protected.
Practice What You Preach: Security beyond Your Services
A reputation for delivering security can’t stop at “protecting your clients.” Word travels fast, and what goes into a client’s mind when they hear you couldn’t protect your internal systems and processes?
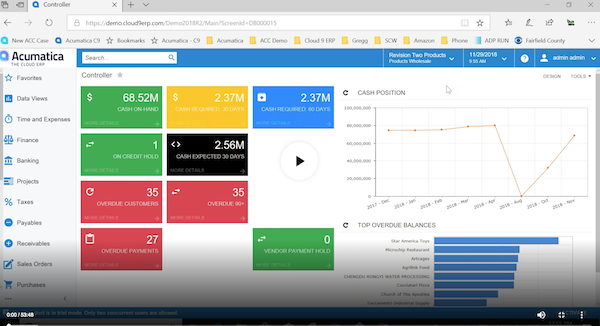
If you’re going to talk the talk when it comes to security, you need to walk the walk. Modern software from Cloud 9 ERP Solutions, like Acumatica, is designed to mitigate the threats to the back office of today’s AV firm. Built in the cloud, this solution helps you to practice what you preach. Learn more about our solutions for AV companies.
Cloud 9 ERP Solutions specializes in configuring and delivering this solution for AV/IT firms including M3 Technologies Group and more, and we would love to help you as well. Let’s get in touch.
Watch Now: How to Leverage Business Software for AV + Network Cabling Service Companies
Additional AV Resources
Don't Let Distancing Derail Your AV Firm: Now is the Perfect Time for an ERP Upgrade
Why Cloud ERP is a Necessity for the Transformed AV Firm
Challenges in Recurring Revenue for AV Firms